![Neuroscience Meets Cryptography: Designing Crypto Primitives Secure Against Rubber Hose Attacks - [PDF Document] Neuroscience Meets Cryptography: Designing Crypto Primitives Secure Against Rubber Hose Attacks - [PDF Document]](https://cdn.cupdf.com/img/1200x630/reader020/image/20190628/55a4f1901a28ab3d038b45e9.png)
Neuroscience Meets Cryptography: Designing Crypto Primitives Secure Against Rubber Hose Attacks - [PDF Document]
![PDF] Neuroscience Meets Cryptography: Designing Crypto Primitives Secure Against Rubber Hose Attacks | Semantic Scholar PDF] Neuroscience Meets Cryptography: Designing Crypto Primitives Secure Against Rubber Hose Attacks | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/b626cc084862c80fa51792946dce8debb34af465/8-Table1-1.png)
PDF] Neuroscience Meets Cryptography: Designing Crypto Primitives Secure Against Rubber Hose Attacks | Semantic Scholar
Reframing how you think about the concept of “managing your private keys” | by Corey Petty | The Bitcoin Podcast Network | Medium

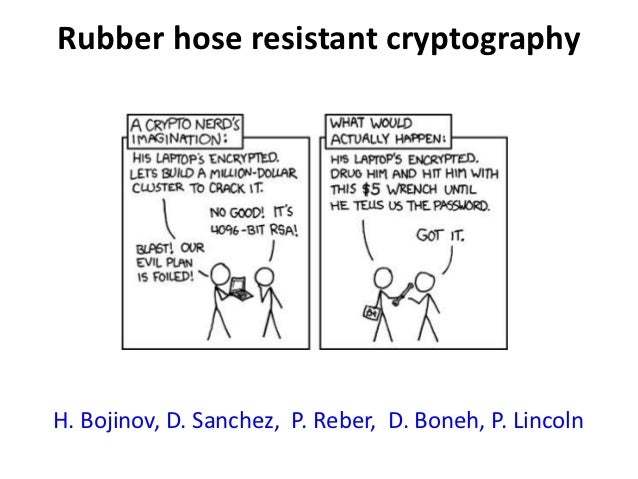
Neuroscience Meets Cryptography: Crypto Primitives Secure Against Rubber Hose Attacks | May 2014 | Communications of the ACM

Rubberhose cryptography and the idea behind Wikileaks: Julian Assange as a physics student | Cryptography, Physics, Student

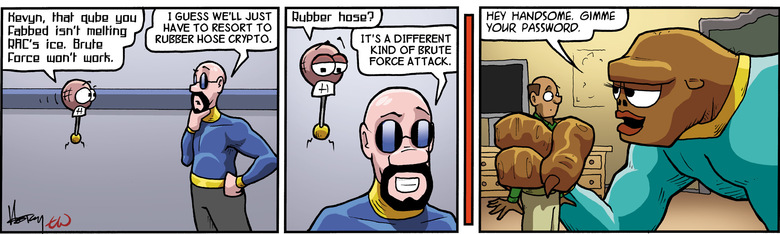
Anonymous Ghostwriters - Rubber Hose Cryptography works by filling the entire hard drive with random characters that are indistinguishable from encrypted data. The file system then takes each archive of real data

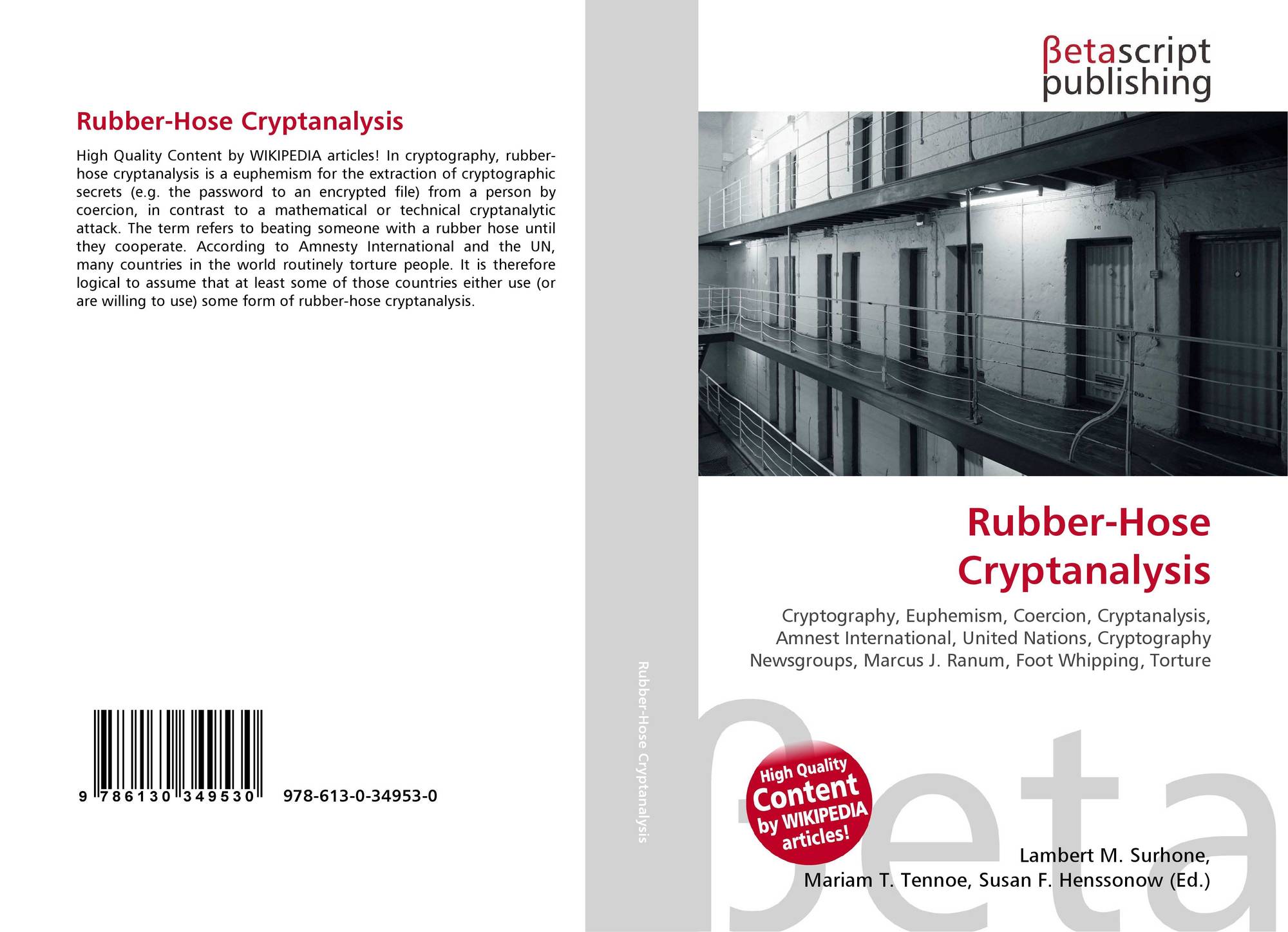
Rubber-Hose Cryptanalysis | Surhone, Lambert M., Timpledon, Miriam T., Marseken, Susan F. |本 | 通販 | Amazon

טוויטר \ Peter Leimbigler בטוויטר: "@austwitnerd @ZachWeiner Conventionally known as rubber-hose cryptanalysis, which is very computationally inexpensive: https://t.co/ZpxKVWWQBh"